Your Managed IT Blog
Email security is essential due to the increasing sophistication of cyberattacks, with 95% of IT leaders noting rising complexity. To protect sensitive data, users should adopt strong passwords, enable two-factor authentication, be cautious with links and attachments, keep software updated, use encryption, and monitor email activity for suspicious actions.
These days, everything is connected—including the software your business runs on, whether it’s installed on your servers or in the cloud. That’s why it's crucial to protect the whole process that develops and delivers your software. Every single step, from the tools developers use to the way updates are pushed out, plays a role in keeping things secure. If any part of this process is compromised, the impact could be severe. So, how do you avoid something happening to you? Let’s dive into why securing your software supply chain is super important.
The NIST Cybersecurity Framework (CSF) helps companies of all sizes fight cybercrime. They just released a supercharged version, NIST CSF 2.0! The Big Five: Identify, Protect, Detect, Respond and Recover. These are the essential steps to take to keep your data safe. Want to identify your vulnerabilities and create a budget-friendly security plan? Schedule a cybersecurity assessment with us today! We'll help you identify your digital assets and weaknesses, then work with you on a plan to keep your data safe.
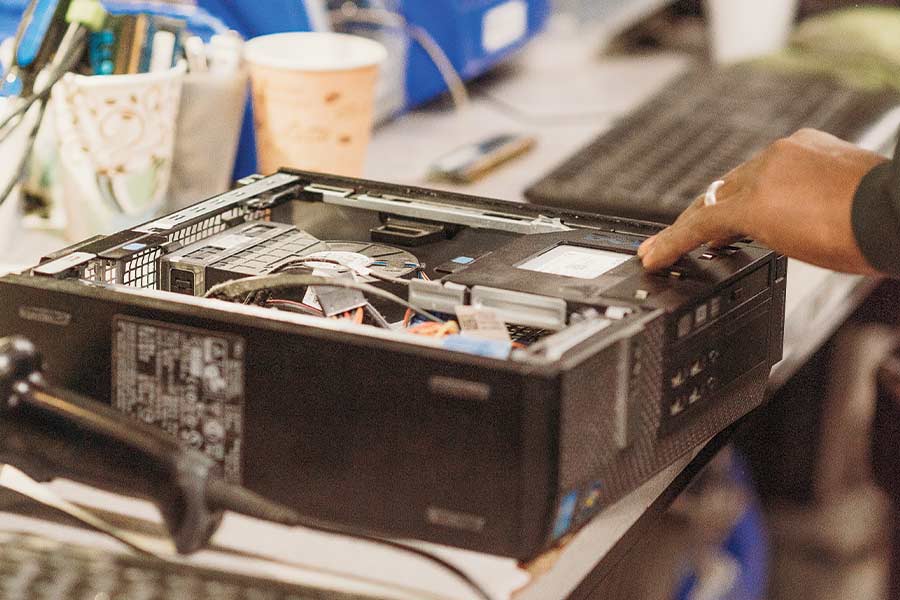
The life cycle of electronic devices is shrinking, leading to a growing mountain of e-waste. Computer recycling and the recycling […]
Emotet, a notorious malware that has been used for years to conduct large-scale email phishing campaigns, is back and causing […]
Endpoints are a large part of an organization’s network and IT infrastructure. This is a collection of computers, mobile devices, servers and smart devices. Like all his IoT devices, […]